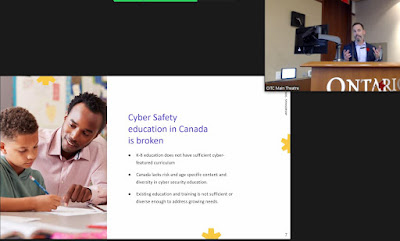
The Problem: Canada's Cyber-education system is broken - or doesn't exist at all
I've been ruminating on this since virtually attending the "How to protect our children in an increasingly digital and online world" meeting by Economic Development Ontario and the Canadian Trade commission a couple of weeks ago. James Hayes from Cyber Legends is a man on a mission. His keynote was both insightful and frustrating - the main point being that Ontario (and by extension Canada)'s cyber-education ecosystem is broken. I'd go so far as to say that in most places it doesn't exist at all; broken implies that there was something there to begin with.The Problem: cybersecurity, cybersafety and online privacy are barely mentioned in Canadian school curriculum and educators are some of the least digitally experienced professionals able to resolve this skills crisis
In Ontario we've mandated mandatory eLearning for all students, but cybersecurity only just got into the computer studies curriculum in this year's rewrite, and what's there is thin (it immediately devolves into personal online data awareness and ignores the many interesting technical specialities in cybersecurity). This optional course doesn't run in most high schools (it was cancelled locally in mine), so this one mention isn't seen by most students.
Many other provinces don't mention cybersecurity at all even as they all depend on it every day with networked education technology delivering material in every classroom. Cyberskills are now essential skills if we want to keep the learning happening, but aren't treated that way in our education systems. New Brunswick is the exception with a full cyber-learning pathway for students interested in heading into the field professionally. Why does that matter? There is a global shortage of cybersecurity professionals, so Canada's usual approach of immigrating in solutions to its education failings won't work in this case.
 |
| James mentioned teacher cyber-illiteracy in his keynote as well. There are solutions like CyberBytes that offer upskilling... |
The Problem: we're happy to make online edtech solutions mandatory (usually as a cost cutting measure) but a surprising percentage of the people doing it don't think they should be held legally responsible for its safe delivery
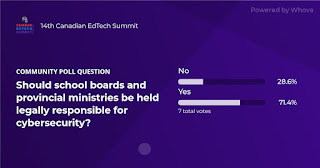 I expected the people delivering online edtech (school boards, ministries, not-for-profits and private edtech companies) to recognize that cybersecurity is very much their responsibility if their technology is vulnerable online, especially if they are going to demand that students use online learning tools. This should be especially obvious when our 'clients' are vulnerable sector children whose safety should be a primary concern.
I expected the people delivering online edtech (school boards, ministries, not-for-profits and private edtech companies) to recognize that cybersecurity is very much their responsibility if their technology is vulnerable online, especially if they are going to demand that students use online learning tools. This should be especially obvious when our 'clients' are vulnerable sector children whose safety should be a primary concern.
Most did recognize the importance of taking responsibility for their technology delivery, but I'd love to have a chat with the quarter or so who thought they should be putting student learning online while bearing no legal responsibility for it. One of those people could well be managing your local school board's technology department.
If we've got a problem with the people delivering online edtech understanding that they are responsible for cybersecurity, we need to back the bus up and clarify those responsibilities with policy - legally binding policy. I recently saw a memo which said data privacy wasn't even a paid job in the school board and is done outside of regular work responsibilities by IT staff, most of whom have no cybersecurity experience. Until we begin taking public sector cybersecurity seriously we will continue to see our public services being disrupted by breaches and system failures.
The Problem: Public services in Canada are siloed bureaucracies that are difficult to work with
 |
| This isn't just an education problem, it's a CANADA problem. Canada's history hasn't produced a culture that can collaborate against asymmetrical global threats. |
There are not for profits and businesses in Canada who are attempting to provide solutions to Canada's ongoing cyber-education failures, but attempting to engage with any public service in Canada is a a difficult prospect. If you talk to the ministries they hold up their hands and say they only manage the funding and not the implementation of cybersecurity solutions. If you talk to the regional school boards they say that they aren't provided resources to do it.
In Canada's uncoordinated cyber policy landscape I suspect it's easier to play victim even as you assume greater cyber risk pushing user data into the cloud than it is to develop a coordinated response to this very asymmetrical problem. These gaps in responsibility make it easy for the people paid to protect student data to point the finger at each other rather than solve the problem, even as breach after breach occurs.
 |
| Canada's failure to coordinate cyber response is recognized as an problem globally. |
Cybersecurity in public education is dangerously under-prioritized even as we continue the rush to cloud based edtech solutions in an attempt to save money. On top of that a surprising percentage of the people delivering these solutions don't think they should be held legally responsible for its safe delivery. This deadlock suggests that we need policy that not only enforces best cybersecurity practices in education, but also makes resources for it a requirement rather than a politically motivated shell game.
But the fix needs to go further in education because we also have a responsibility for providing graduates with opportunities to learn the skills they need to survive in a rapidly changing world; something we're not doing as many jurisdictions continue to studiously ignore cyber education and digital skills in general. The key piece to this puzzle is policy that creates a responsive, responsible Canadian cybereducation system. In aligning resources to create cybersecure online learning we might also usher in a new era of relevant, richer digital skills development.
The Solution: A Viable 21st Century Canadian Digital Education Ecosystem
As both James and Kyle mentioned in their talks, technology moves so quickly that large public services are always going to struggle to keep up, but an agile edtech sector could help with that. Startups and small businesses can pivot to keep up with technology emergence in a way that larger organizations struggle with - that's why Google and the rest buy agility rather than trying to produce it in-house. The problem has been Canada's pigeon hole approach which doesn't aim to produce a coherent ecosystem of interrelated programs that provide a comprehensive Canadian shield.
As mentioned previously, the issue of regional school boards and provincial ministries making it difficult for anyone outside of these insular systems from collaborating with them is a key problem. We can't leverage digitally literate industry partners if they have no way to effectively communicate with education delivery systems.
The solution is to connect the federal government with the Council of Ministers of Education, Canada and The Insurance Bureau of Canada and design a centralized approval process that connects Canadian not for profits and industry edtech expertise with provincial ministries and clears the way for access to credible cybereducation materials through direct internal communications channels with education systems. Instead of individual boards doing cyber badly, a national partnership with a wide range of technology specializations and strengths would work together to build solutions at scale while also ensuring that these solutions are prioritized with mandatory funding. This relationship would also prompt meaningful updates to curriculum instead of the current 'in a bubble' approach that produces material well short of what is needed to prepare graduates for our technically challenging future.
 |
| I made this graphic after last year's CPI conference at University of Waterloo, where I first met James, Cheryl and Cyber Legends. |
This ecosystem would reward collaboration. Members would only be accepted if they are producing complementary resources that create a full range of learning opportunities to all aspects of our increasingly digital world across all subjects, including cybersecurity. This nationally curated resource allows teachers from all corners of the country to develop meaningful digital skills, including the difficult ones to deliver like cybersecurity. This equity of access to resources would end nationally embarrassing PISA results that prevent smaller provincial education systems who lack resources from producing results below the world average. Members of Canada's edtech program would find funding easier and be able to work with partners who ensure that their programs are successfully integrated and in a constant state of improvement in order to keep up with the impressive rate of technological change we're all dealing with. This would also give those providing federal funding clear guidelines for who they should be supporting.
The stick would come through policy changes that are both legal and regulatory. Any school board (and by association ministry) not making use of these secure, partner provided resources for improving student data protection would find themselves both liable for any breaches, and also uninsured. Educational cybersecurity would no longer be a political blame game. Local implementation would still very much remain the purview of school districts, and ministries would remain very much in charge of funding their province or territory, but with focused federal support many of the associated expenses would be reduced through the centralization of resources. These savings would also be a carrot. With national cyber standards and partnerships that leverage the strengths of all members of Canada's education ecosystem (federal government, private industry, national not for profit, education ministries, and local school boards), Canadian students would enjoy access to more Canadian made digital learning opportunities that raise digital fluency in a meaningful way, and they could do this while also exploring cybersecurity in a way that creates a more secure Canada. Imagine what all these cyber-aware students could do for our national security. It's the only solution we have that scales to meet the problem. Those students go home and raise cyberawareness in their families and communities, reducing the main reason for successful cyberattacks.
We have a habit of regionalizing our approaches to government in Canada, but in the face of wildly asymmetrical threats like cybercrime and (increasingly) international cyber espionage, we need to push back against this culture and build a collaborative defence. In doing so we would also create much richer digital learning opportunities in our schools that would make Canada more secure and competitive in the networked, global economy.
The Solution: collaboration doesn't end locally, regionally or even nationally in Canada
I'm attending The Global Forum for Cyber Excellence's inaugural Global Conference on Cyber Capacity Building in Accra, Ghana at the end of November.
I'm presenting a research paper a former student and CyberTitan (Louise Turner) and I have written about the disruption quantum computing will cause to cybersecurity encryption in the coming years. Doing this research with Louise has been both eye opening and very intellectually satisfying, but after 20+ years in the classroom I'm still very much a cyber-educator first and a cyber researcher second. It's why I invited one of the next generation of cyber professionals to write the paper with me.
Looking at the program for the conference, the lack of talent and focus on developing cyberskills both in the population and in those interested in pursuing work in the industry isn't a Canada only problem, it's a global one. If we can repair Canada's internal cyber-education system, we can then work with international partners to help them do the same. The cyber battlefield inherently favours the anonymity of hackers damaging our systems with impunity for their own gain, but through collaboration the defenders could become mighty. A cyber-aware population would be foundational for reducing cyberattacks in our public services.
As the GFCE so eloquently puts it: "Nations should work together and support each other with these capabilities, so that no country is left behind in their digital evolution. After all, a chain is only as strong as the weakest link." Look for the Accra Call: a global action framework that supports countries in strengthening their cyber resilience being announced during the conference.